If running the diagnostics for the Brightmetrics Agents results in an error about SSL connectivity, there is usually one of two problems it could be.
Problem 1: Windows Server 2003 missing SHA2 support
If the server is running Windows Server 2003 and does not have the latest Windows updates enabling support for SHA2 SSL certificates, you can test its SHA2 support by visiting https://webapp.brightmetrics.com/ using IE on the server.
IE uses the same Windows HTTPS support as the Brightmetrics agent, making it a representative test. Chrome or Firefox would not be, as they have their own internal HTTPS support.
- If you are able to see the login page, the system has SHA2 support.
- If you get a communications error like "Internet Explorer cannot display the webpage," it probably lacks SHA2 support.
If you cannot install all current Windows security updates for some reason, you can install just Microsoft security update 2868626.
Problem 2: Proxy or content filter intercepting HTTPS
A proxy or content filter may be intercepting the HTTPS connection and re-encrypting it with its own certificate authority (CA). Often an Active Directory Group Policy will push the content filter's CA into each user's profile as a trusted root CA, but a corresponding computer policy to push the content filter's CA into each computer's trusted root CA has not been established — therefore any services running on the server are not able to establish trust.
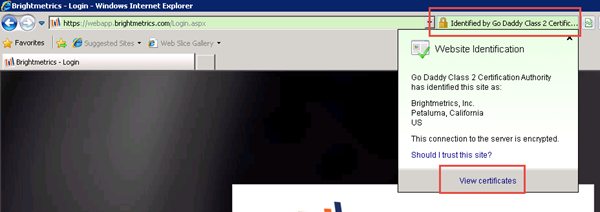
This problem can also be identified using IE on the server. Visit https://webapp.brightmetrics.com/ using IE and observe the security information next to the address bar.
- You should see the green address bar indicating an Extended Verification (EV) SSL certificate is in use.
- If you see only the lock icon, that is the first clue that the SSL certificate is being replaced.
To verify, click on the security icon and select View certificates:
In the certificate dialog box, click Certification Path and ensure that the certificate chains up to the "Go Daddy Class 2 Certification Authority" as shown below:

If it chains up instead to a root CA that looks like it may be from your content filter, that is the problem being described.
The proper solution is for IT staff to ensure that the content filter's CA is a trusted root CA on all computers in the organization, just as it is for all users. However, if a quicker solution is necessary, the certificate can be exported and imported into the computer's trusted root CA list. Here's how:
-
1
Click View Certificate with the root CA highlighted. In that dialog box, click the Details tab and click Copy to file. Follow the wizard to export the certificate in DER format to a file on your desktop.

-
2
From the Start menu, click Run and enter mmc.

-
3
In the MMC application, choose File then Add/Remove Snap-in.

-
4
From the available snap-ins list, choose Certificates and click Add.

-
5
When asked which account to manage certificates for, choose Computer account, then Local Computer.


-
6
Click OK to close the dialog. -
7
Back in the MMC application, under Certificates, right-click Trusted Root Certification Authorities, choose All Tasks, then Import…

-
8
Follow the wizard to select and import the file exported to the desktop in step 1. Make sure the Certificate store is set to Trusted Root Certification Authorities.

That's all. The Brightmetrics agent, and any other services running locally on the server, should now be able to trust SSL certificates created by your content filter.
Didn't find what you're looking for, or have questions about what you read? Email us at support@brightmetrics.com.